Critical Pacemaker Vulnerability Revealed – Millions of Lives at Risk
A new vulnerability allows hackers to hack into Abbott’s pacemakers using RF waves and fully take control over the running device. How Do Pacemaker Works? Pacemaker are devices that is implanted in the chest or abdomen to…
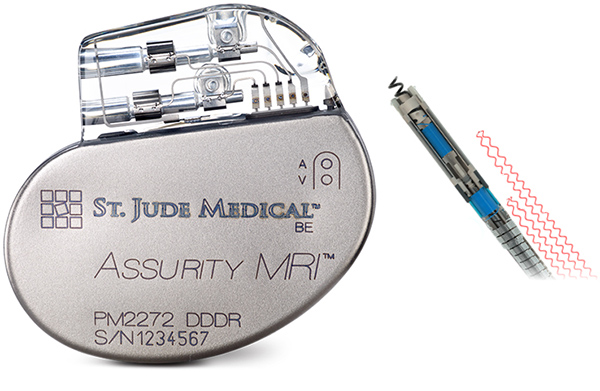
A new vulnerability allows hackers to hack into Abbott’s pacemakers using RF waves and fully take control over the running device.
How Do Pacemaker Works?
Pacemaker are devices that is implanted in the chest or abdomen to help control abnormal heart rhythms. This device uses electrical pulses to prompt the heart to beat at a normal rate.
Devices like Pacemakers and ICDs have have been using radio frequency (RF) to transmit patient’s health status wirelessly to a remote server/bedside transmitter which will send the data to the doctor via internet. These devices works in the MICS (Medical Implant Communication Service) frequency band (between 402 and 405 MHz) and pair with the monitor using the pacemaker’s serial number and/or device model number.
These implantable device and monitor can communicate with each other over a range of up to 50 feet, which could be increased by using high gain antenna. This wireless RF link can also be used to remotely maintain the pacemaker, updation of firmware etc so that these devices can be accessed without another surgery.
How Pacemakers can be Exploited?
These little wireless life sustaining devices are found to have real cyber security vulnerabilities that are placing millions life at risk. It was observed that a hacker with in the range of the radio, could take complete control over the running pacemaker.
“If there were a successful attack, an unauthorized individual (i.e., a nearby attacker) could gain access and issue commands to the implanted medical device through radio frequency (RF) transmission capability, and those unauthorized commands could modify device settings (e.g., stop pacing) or impact device functionality,” said Abbott in an open letter to doctors
Once the connection is established over the RF link a hacker could easily read and write memory, rewrite firmware, modify its parameters and even kill the device from functioning normally.
How It To Protect Yourself?
In order to patch these to patients are told to visit their doctors and update the firmware of the vulnerable pacemakers as soon as possible.
The firmware update process takes approximately 3 minutes to complete, and during this time, the device will operate in back‐up mode (VVI pacing at 67 bpm), and essential, life sustaining features remain available. At the completion of the update, the device will return to its
pre‐update settings.
It is also said that, based on our previous firmware update experience, as with any software update, there is a very low rate of malfunction resulting from the update. These risks (and their associated rates) include
but are not limited to reloading of previous firmware version due to incomplete update (0.161%), loss of currently programmed device settings (0.023%), complete loss of device functionality (0.003%), and loss of diagnostic data (not reported).








This helps. Cheers!
This may be the proper weblog for everyone who wishes to be familiar with this topic. You are aware of so much its nearly hard to argue to you (not that I really would want…HaHa). You certainly put a brand new spin with a topic thats been discussing for a long time. Wonderful stuff, just great!
Appreciating the time and energy you put into your blog and in depth information you provide. It’s good to come across a blog every once in a while that isn’t the same unwanted rehashed information. Excellent read! I’ve saved your site and I’m adding your RSS feeds to my Google account. ebedkcfeaede