ROPEMAKER – Modify E-Mail even after it is sent
A new technique allows attackers to modify the contents of an E-Mail even after it is sent and received by the recipient. The new exploit named ROPEMAKER (Remotely Originated Post-delivery Email Manipulation Attacks Keeping Email Risky) is…
A new technique allows attackers to modify the contents of an E-Mail even after it is sent and received by the recipient. The new exploit named ROPEMAKER (Remotely Originated Post-delivery Email Manipulation Attacks Keeping Email Risky) is an easy to use exploit that can change the URL in a delivered Email or swap normal text to a URL or edit the whole text in an Email.
How Does it Work?
This can be exploited without having direct access to the Email account or the targets inbox. This attack is done by manipulating CSS (Cascading Style Sheets) and HTML. Even though CSS improves the visual environments, it have now become an attack vector.
Below is the demonstration of a simple ROPEMAKER
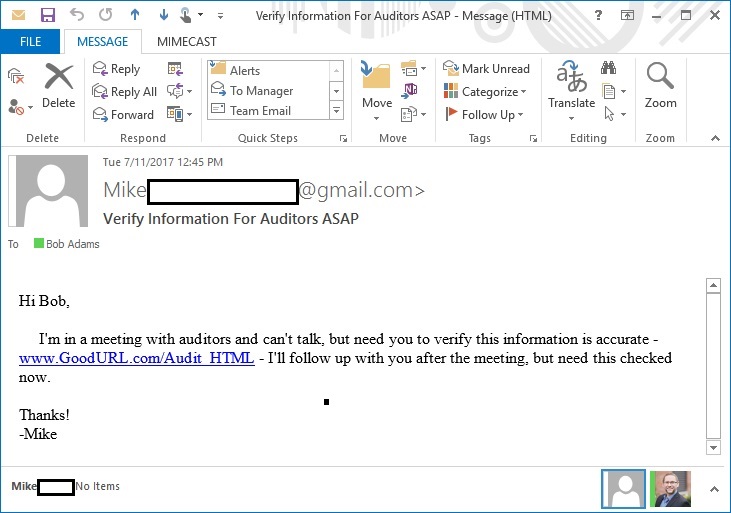
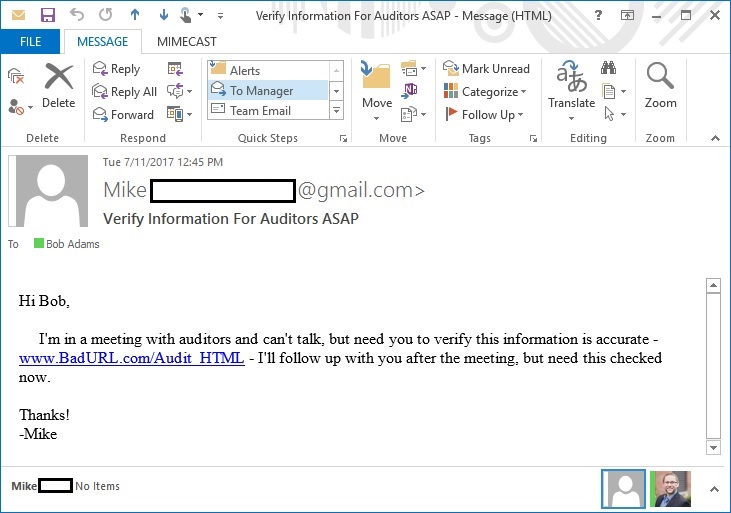
In this example, an email with a ‘good URL’ is switched to ‘bad URL’ by an attacker. This is done by editing the remote CSS from which the email gets its display style. In real world, these URLs in the mail can be changed to phishing URLs which can cause which can be used for targeted attacks against an individual or a group.
For more Details check out the documentation published by mimecast.



Wonderful goods from you, man. I’ve keep in mind your stuff prior to and
you are simply too fantastic. I really like what you have got here, really like what you’re
saying and the best way during which you are saying it.
You’re making it enjoyable and you continue to care for to
keep it smart. I can not wait to learn much more from
you. This is actually a terrific site.
Thanks buddy. Will do the best I can
That is the best blog for anybody who wants to search out out about this topic. You realize so much its virtually onerous to argue with you (not that I actually would want…HaHa). You undoubtedly put a brand new spin on a topic thats been written about for years. Great stuff, just nice!