Hacker Hardware Tools | Computer Hacker Equipment for Hardware Hacking 2020
Hacker Hardware Tools “S in IOT stands for security”. When you look deeper into an IOT device or any embedded device for that matter, what do you see? You see windows of opportunities. Opportunities to modify it….
Hacker Hardware Tools
“S in IOT stands for security”. When you look deeper into an IOT device or any embedded device for that matter, what do you see? You see windows of opportunities. Opportunities to modify it. To edit it. To exploit it. To hack it. IOT devices are full of vulnerabilities. In this post you will find a list of hardware hacking tools which can be used for easily hacking communication protocols such as Wi-Fi Bluetooth and other RF communication protocols as well as devices such as PCs, laptops and androids without much scripting or coding.
Hardware Hacking Tools
These are really cheap and easily accessible hacking tools which is available in Amazon. Amazon link is provided with each devices so that you can easily purchase them online.

So far, Kali Linux has been the best and most widely Operating System, filled with an awesome collection of hacking tools which can be used to Web Application penetration testing, network security testing, WiFi attacks; best of its kind. It is the most famous and most useful Operating System used by security enthusiasts, hackers – both white hat and black hat, as well as hobbyists who like to tinker around with Linux OS.
Computer Hacker Equipment for Hardware Hacking
But there is a small problem with the Linux distributions. There is only smaller selection of hardware components that have driver support for Linux. So many devices such as USB Adapters, development boards as well as devices like printers, scanners etc does not have driver support for windows. Of course the linux community is developing and adding newer drivers with every release. But still older devices remain unchecked.
Due to these reasons, finding the right device for hacking which works in Kali Linux can be a headache.
Recently Kali Linux 2020.1 was released which updated the worlds best penetration testing OS with some neat hardware support including some WiFi Adapters to play around with WiFi networks. Here are a list of Top WiFi adapters that are 100% compatible with Latest Kali Linux, that can go into monitor mode, inject packets and perform everything that is needed for a full fledged WiFi Penetration Testing.
If you are an ethical hacker, interested in intrusion testing and cyber security, and you are interested in hacking devices, You should have these smart hacking device and tools and you should know how each of them works. you can easily start hacking with this smart devices with very little or no coding. most of them are plug-and-play which means you can simply connect these hacking tools to your device and start playing with them. The Best Collection of Hacker Hardware Tools .
Here we will be showing you a list of Top Hacking Tools – best of its kind. You could use to hack computer, hardware parts, WiFi, BlueTooth and other RF communication.
Updated : April 2019
UberTooth One
The Ubertooth One is one of the best tools you can find online for Bluetooth hacking. It is an open source development board that works in 2.4 GHz Frequency which is widely used for Bluetooth hacking. Of course there are some other devices which can be used for monitoring Bluetooth traffic. But they all cost over $10,000. This is a compact device which can be connected to your computer via USB port.
Even though it looks like a naked bluetooth USB dongle, it can do a lot more than that. Just like you capture WiFi packets using a Wi-Fi adapter you can sleep the data which is being transmitted from a Bluetooth device using ubertooth.
Product description
The Ubertooth One is an open source 2.4 GHz wireless development platform suitable for Bluetooth experimentation. Based on the powerful LPC175x ARM Cortex-M3 microcontroller with full-speed USB 2.0, the Ubertooth One is a great way to develop custom Class 1 comparable Bluetooth devices. The entire board is only****two and a half inches long with a USB-A connector at one end and an RP-SMA connector at the other.
One thing that sets the Ubertooth apart from other Bluetooth development platforms is that it’s capable of not only sending and receiving 2.4 GHz signals, but can also operate in monitor mode, monitoring Bluetooth traffic in real-time. This operating mode has been present in low-cost WiFi modules for years and has found myriad uses in research, development and security auditing but no such solution existed for the Bluetooth standard until now. Also, because it’s a fully open-source platform (software and hardware), the schematics and code are readily available for all of your hacking needs.
Dimensions: 61.75mm x 19mm (2.43″ x 0.75″)
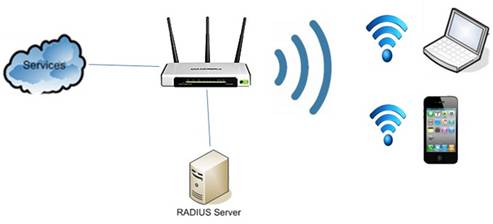
Alfa AWUS036NHA USB WiFi Adapter
Alpha is the prime of networking devices such as wireless adaptors network cards and Wi-Fi Antennas. This is one of the most widely used USB Wi-Fi adaptor available in the market. Sleek and beautiful, curvy and black. Of course there is a wide variety of USB Wi-Fi adaptor was in the market but what makes this the best choice for hackers? What makes it one of the best Hacker Hardware Tools?
First reason is this is compatible with almost all the Linux distributions. You can simply plug the USB Wi-Fi adaptor to your device and start using it right away.
Second this one uses another chipset Atheros, that supports all 6 WiFi modes. It is observed that the success rate of various injection attacks which is performed using this Wi-Fi adaptor is much greater than any other USB WiFi adaptor available.
Product description
* Includes a 9dBi original Alfa antenna
* Compatible with any Brand 802.11g or 802.11n Router Using 2.4ghz Wavelength and supports MIMO (Multiple Input Multiple Output)
* High speed transfer TX data rate up to 150 MbpsAWUS036NHA is an IEEE 802.11b/g/n Wireless USB adapter. It provides users to launch IEEE 802.11b/g/n wireless network at 150 Mbps in the 2.4GHz band, which is also compatible with IEEE 802.11b/g wireless devices at 54 Mbps. AWUS036NHA is compatible to higher-performance, multi-stream, MIMO-based 802.11n, and are available in reference designs to serve the networking, PC and consumer electronics markets. AWUS036NHA includes a convenient Utility that scans for available networks on Windows XP and saves preferred networks that users are usually connected with. Security encryption can also be configured by this utility.
Compatibility
– Any PC or Laptop with a USB port, 733MHz CPU, and 64MB Memory
– Any brand 802.11g or 802.11n router using 2.4ghz wavelength
– Windows 2000, 2003, XP Home/Pro/64-Bit, Vista 32-Bit/64-Bit, Windows 7
– NOT COMPATIBLE with Xbox 360, PS3, Blu-Ray Players, Roku Boxes, or any device that does not run an Operating System. Also will not work with Dual Band Routers that only broadcast N speeds on 5ghz wavelength – it is also not compatible with any Apple MacSecurity
This adapter provides state of the art standards-based security features: WPA/WPA2, IEEE802.1X, 64/128-bit WEP. With these enhanced security features, you can encrypt your data and only allow authorized users to access your wireless network.* Data Rate 802.11b: UP to 11Mbps / 802.11g: UP to 54Mbps / 802.11n: UP to 150Mbps
* Antenna Type2.4Ghz RP-SMA connector
* Chipset AtherosAR9271
* Security WEP 64/128, 802.1X support, Wi-Fi Protected Access (WPA), WPA-PSK, WPA II-PSK, Cisco CCX support, WAPI-PSK,WAPI-CERT
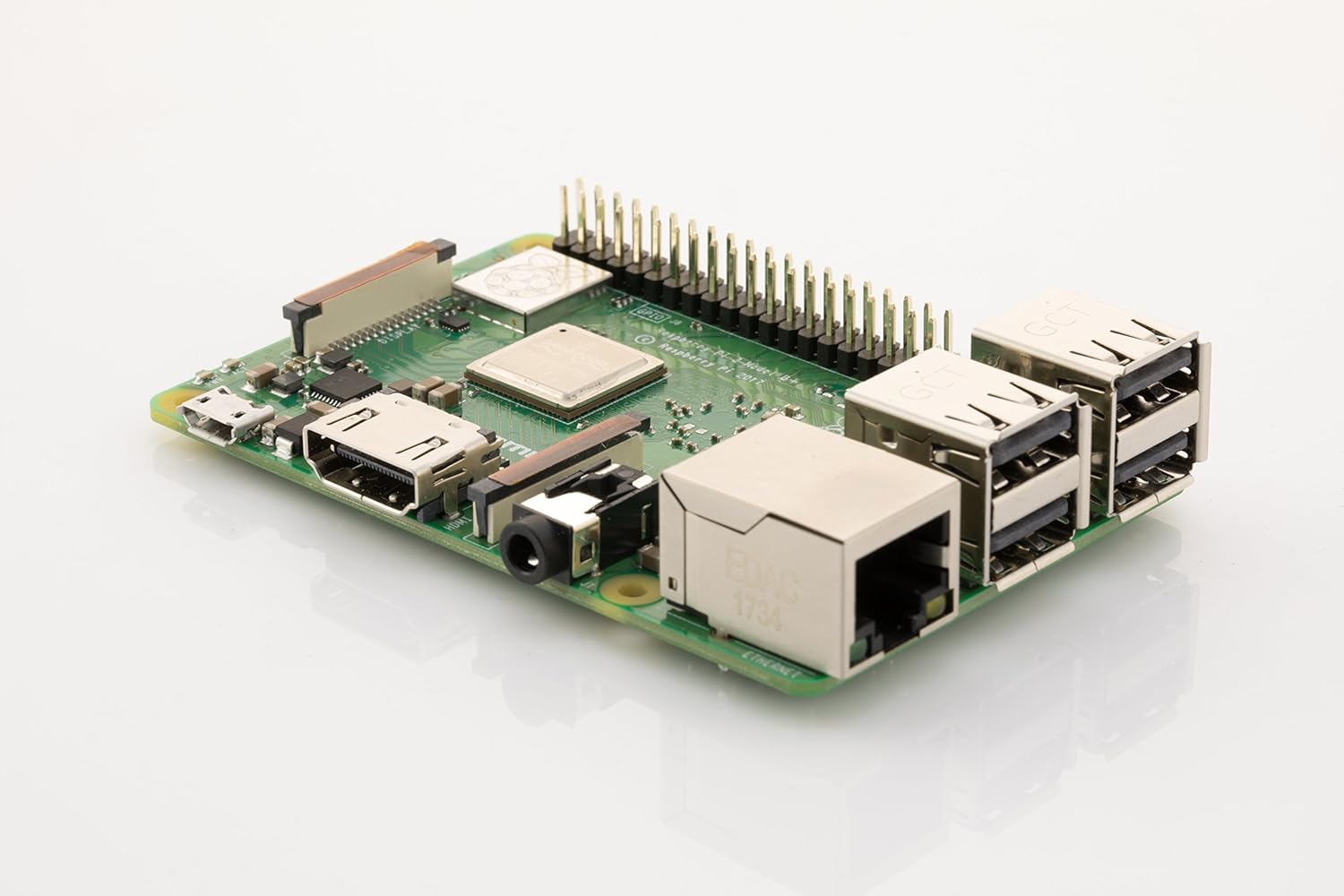
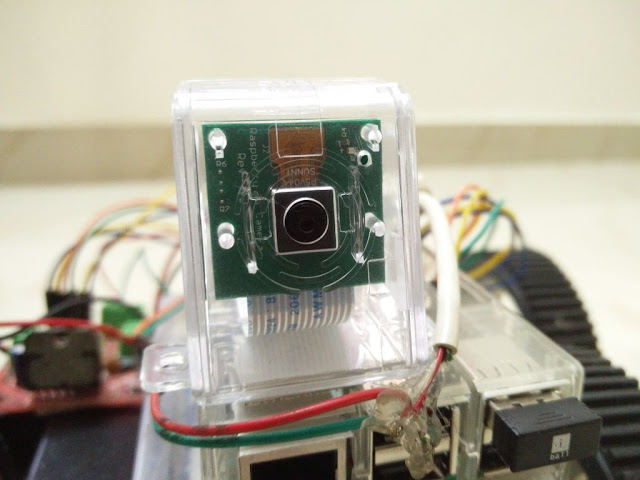
Raspberry Pi
If you have decided to learn hacking you would be wondering what to learn first. When you are beginning to learn ethical hacking the most likely operating system you will be using is Kali Linux. This is because there is a huge community of beginners as well as people who have a lot of experience in the field of hacking and due to that reason there is a lot of help out there in the community. Kali Linux have a lot of hacking tools which can be used for hacking web applications networks wireless networks hardware etc. So where will you install this Kali Linux?
Well it is not a good idea to install a hacking operating system in a device that you use for your everyday life. A much better way is to install the hacking operating system on a different computer this isolating your personal data.
The best device for you to install Kali Linux to learn ethical hacking is a Raspberry Pi. This is great for anybody learning about hacking because it runs Kali Linux and allows you to see this as a Lego peace and create a prototype for an idea that relies unplugging a couple of things into this and making it work. It allows you to segment away all the experimental things from the things that you really want to keep safe and if it get fried and become corrupted, you can simply replace the SD card or format the SD card or even just get a new Raspberry Pi which is really really cheap.
Product description
New Original Raspberry Pi 3 Model B+ Built-in Broadcom 1.4GHz quad-core 64 bit processor with Low Energy On-Board Wifi Bluetooth and USB Port
Built on the latest Broadcom 2837 ARMv8 64 bit processor, Raspberry Pi 3 Model B+ is faster and more powerful than its predecessors. It has improved power management to support more powerful external USB devices and now comes with built-in wireless and Bluetooth connectivity. To take full advantage of the improved power management on the Raspberry Pi 3 and provide support for even more powerful devices on the USB ports, a 2.5A adapter is required.
Technical Specifications:
– Broadcom BCM2837BO 64 bit ARMv8 QUAD Core A53 64bit Processor powered Single Board Computer run at 1.4GHz
– 1GB RAM – BCM43143 WiFi on board
– Bluetooth Low Energy (BLE) on board
– 40 pin extended GPIO – 4 x USB2 ports
– 4 pole Stereo output and Composite video port
– Full size HDMI
– CSI camera port for connecting the Raspberry
Pi camera – DSI display port for connecting the Raspberry
Pi touch screen display – MicroSD port for loading your operating system and storing data
– Upgraded switched Micro USB power source (now supports up to 2.5 Amps.Package Contents :
– 1x Raspberry Pi 3 Model B+
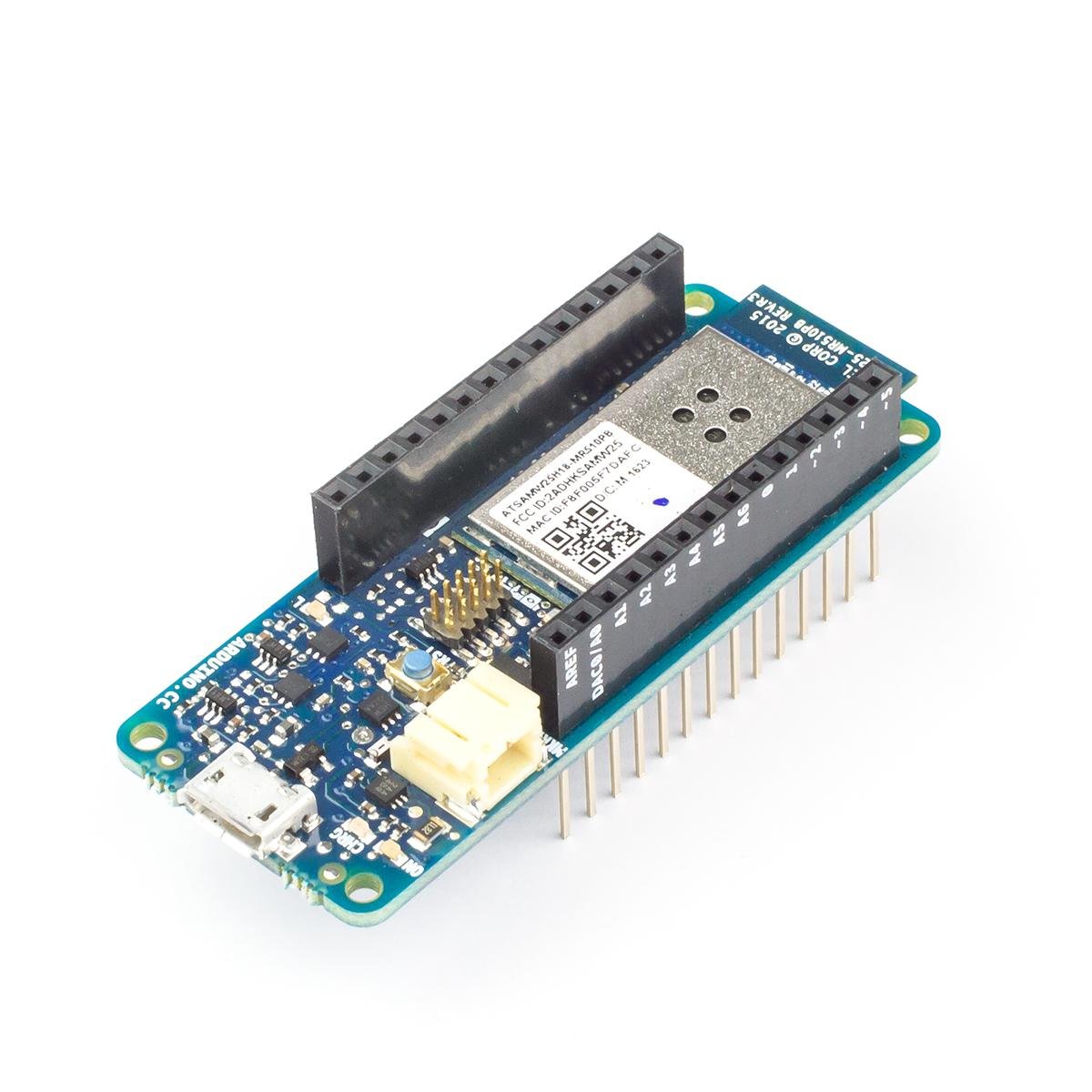
Arduino MKR1000
This is a super cool or do you know about which have a built in Wi-Fi chipset. This device is specifically designed for projects that allows you to connect your devices to internet. Like most of the arduino boards this board can be powered and programed using the USB port.
This device can be connected to your Wi-Fi network without using any Wi-Fi shield And that’s as a web server. This device can also act as a human interface device like a USB mouse or Keyboard which can send keystrokes to the computer which is connected to it. Sounds familiar? Similar to a rubber ducky.
Attack Demo
Yes you can create a rubber ducky using arduino mkr 1000. Actually this is much better than a rubber ducky. This board can be programmed in such a way that when you connect this Arduino to a computer it will detect this board as a human interface device such as a USB keyboard. One hit get detected as a USB device the arduino board will start to send keystrokes to that computer. you can send whatever things a real keyboard can type using this board.
Moreover this micro controller board will serve a web page in port 80 which can be accessed by any devices in that Local Network. this webpage will be having a list of attacks which can be performed using this board. you can simply select one sit back and enjoy while the Arduino do its work.
Product description
Arduino MKR1000 has been designed to offer a practical and cost effective solution for makers seeking to add Wi-Fi connectivity to their projects with minimal previous experience in networking.It is based on the Atmel ATSAMW25 SoC (System on Chip), that is part of the SmartConnect family of Atmel Wireless devices, specifically designed for IoT projects and devices.
The ATSAMW25 is composed of three main blocks:
- SAMD21 Cortex-M0+ 32bit low power ARM MCU
- WINC1500 low power 2.4GHz IEEE® 802.11 b/g/n Wi-Fi
- ECC508 CryptoAuthentication
The ATSAMW25 includes also a single 1×1 stream PCB Antenna.
The design includes a Li-Po charging circuit that allows the Arduino/Genuino MKR1000 to run on battery power or external 5V, charging the Li-Po battery while running on external power. Switching from one source to the other is done automatically.A good 32 bit computational power similar to the Zero board, the usual rich set of I/O interfaces, low power Wi-Fi with a Cryptochip for secure communication, and the ease of use of the Arduino Software (IDE) for code development and programming. All these features make this board the preferred choice for the emerging IoT battery-powered projects in a compact form factor.The USB port can be used to supply power (5V) to the board.The Arduino MKR1000 is able to run with or without the Li-Po battery connected and has limited power consumption. Tis is ofcourse one of the best hardware hacking tools of all time.
The MKR1000 Wifi module supports certificate SHA-256.
Warning: Unlike most Arduino & Genuino boards, the MKR1000 runs at 3.3V. The maximum voltage that the I/O pins can tolerate is 3.3V. Applying voltages higher than 3.3V to any I/O pin could damage the board. While output to 5V digital devices is possible, bidirectional communication with 5V devices needs proper level shifting.
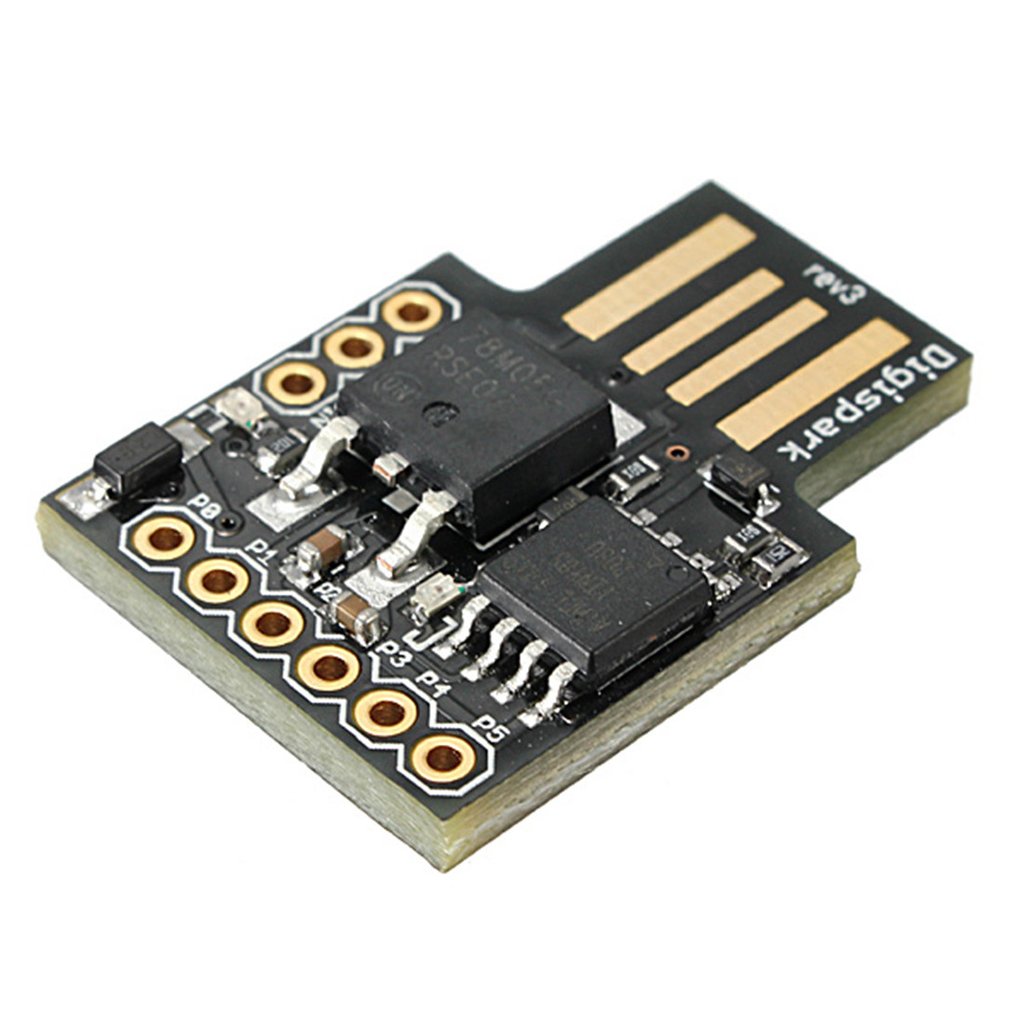
DigiSpark
As a hacker usually know the importance of a micro controller board. like I mentioned in the previous product in Micro controller can be used to simulate a USB human interface device. This one is a compact lightweight micro controller board similar to arduino which can be programmed using arduino IDE.
Attack Demo
You can easily program this device using arduino software and the code is pretty much similar to that. it can send keystrokes at very high speed the use of would even notice that. all you have to do is simply connect this device to the victims machine. And Do you know what the best part is? This hacking tool costs only 1.5 $. This make it one of the best Hacker Hardware Tools available online.
Product description
Support for the Arduino IDE 1.0+ (OSX / Win / Linux)
Power via USB or External Source – 5V or 7 -35V (automatic selection)
On-board 500ma 5V Regulator
Built-in USB(and serial debugging)
6 I/O Pins (2 are used for USB only if your program actively communicates over USB otherwise you can use all 6 even if you are programming via USB)
8k Flash Memory (about 6K after bootloader)
I2C and SPI(vis USI)
PWM on 3 pins (more possible with Software PWM)
ADC on 4 pins
Power LED and Test/ Status LED (on Pin0)
Weight: 4g
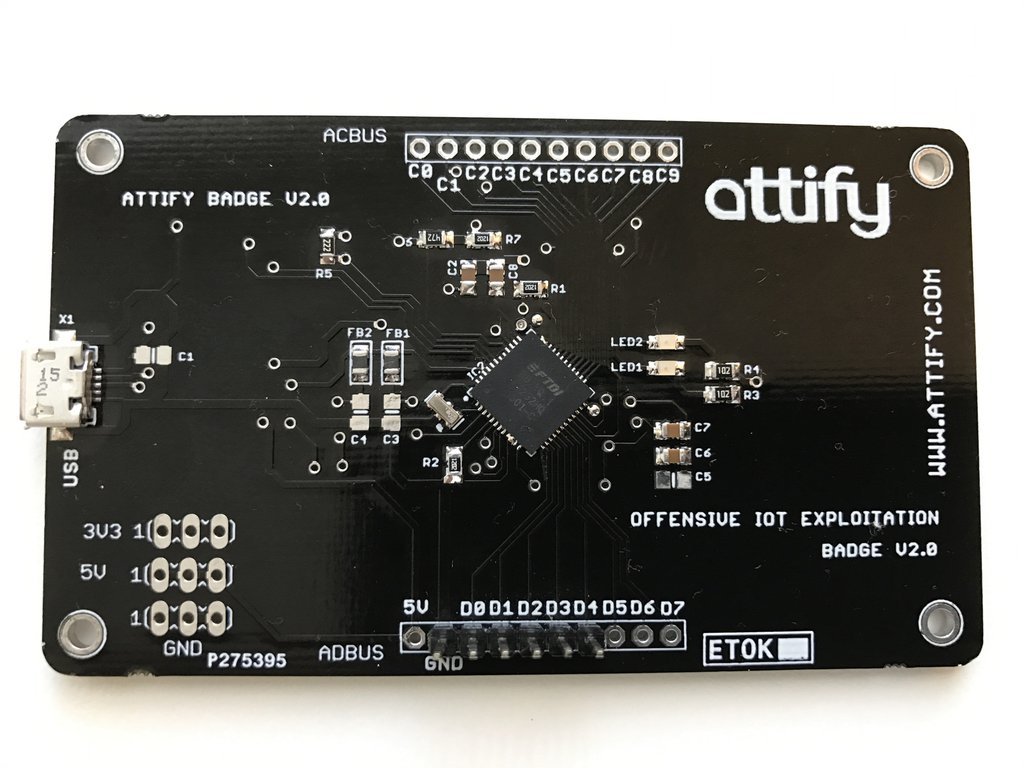
Attify Badge
This is one of the Best Hacking Tools which is designed for iot penetration testing. This one support various types of serial Communication protocols which can be used to connect two variants embedded devices success microcontrollers of iot devices. They also have a debian based Linux OS that have all the tools and scripts necessary for you to get started.
This can be used to perform various attacks like information disclosure memory dumping denial of service and even directly send the various AT two devices causing it to malfunction
Attify badge is a hardware hacking tool that allows you to interact with various hardware interfaces and ports such as UART, SPI, I2C, JTAG, GPIO and so on.
Exploit IoT devices using the Attify Badge as your swiss army knife for hacking hardware devices. This tool was initially developed for the “Offensive IoT Exploitation” training conducted by Attify conducted both real-world and online.
Get this tool and get started on your IoT and Hardware exploitation journey.
Online Mention:
Using UART to get a root shell on an IP Camera
5-Min Tutorial: Gaining Root via UART
SPI and UART Exploitation on an IP Camera using Attify Badge from the IoT Exploitation Learning Kit – Link
Performing JTAG debugging and Exploitation with Attify Badge (PDF – Chinese)
Bluetooth 4.0 Low Energy Micro Adapter – Bluetooth Dongle
This is another bluetooth USB dongle which is supported by most of the Linux distributions. you won’t be able to perform Complex attacks such as sniffing or decoding. but you will be able to do a survey on nearby bluetooth devices enumerate the services and even send simple data packet to them.
this one is really cheap and is compatible with most of the OS. This device is plug and play which means you can simply connect this device to a computer or a Raspberry Pi out of the box and start using it right away.
Product Description
MultiBlue Dongle USB BlueTooth
This is another one of the Best Hacking Tools bluetooth hacking. This device can be connected to another computer via a USB port and then you can use your computer to control the victims computer via bluetooth.
Using this device you can send keystrokes to Android Apple Windows or Linux device using a bluetooth connection. this is very compact and is open mistaken for a USB flash drive and no one will be suspicious.
Convenient to install: MultiBlue Dongle is installed automatically by embedded software in the Dongle without any driver CD
Enables you to input text messages, messenger, note and so on using PC or Laptop keyboard.
Simple One Time Pairing: Once it is paired with your PC or Laptop, it doesn’t need to be paired again next time for use.
Pairing up to 4 Bluetooth devices and controlled by your paired PC or Laptop.
World Patented New Product
Hardware Hacking
Let me ask you a simple question. how to get into hardware hacking? If you are investigating something new or if you want to break into something new If you want to create a tool to explore something You have to do a lot of research online. you have to learn how stuff works. Go to Google. Google is your best friend. There are so many things out there that you can find easily. You can easily learn various protocols, different ways by which devices communicate with each other, different ways by which you can tinker around with the hardware circuits and do things that device is not supposed to do.
When you are looking into hacking hardware, you have to tear down, open it up, get the screws out and understand what’s going on inside. If you cannot understand what’s going on inside that’s ok just look. Eventually, you will start to notice patterns. From there you can step up. You can start hacking them. You can start using hacking tools to modify the protocols and do things whatever you want.
Rate the Products
Did you find this page useful? Help us to improve by rating this page.




![[Solved] Kali Linux Auto Login – The Easy Way](https://hackersgrid.com/wp-content/uploads/2024/02/Enabling-Auto-lin-in-Kali-Linux-768x439.webp)


