New Wave of Ransom Denial of Service – Global Rise in Ransom DDOS Attack
What is RDDOS Attacks? Find out everything you need to about the rising Ransom Denial of Service and how to defend against it.
Rising Trend in Ransom DDOS Attacks in 2021
While DDoS attacks have historically targeted public assets, harming the reputation of an organization through public exposure; healthcare is an exception. These attacks on back-end infrastructure occur on weekdays during business hours, with little activity on weekends or holidays. This influenced daily business operations; such as employee connectivity to cloud-based applications or remote access for those who continued to work from home.
Even though the number of Ransom DDoS attacks remained constant in the first quarter of 2021, their volume increased by 31%, as per Radware’s DDoS Attack Report. Major attacks with a throughput of 10 Gbps or greater, multiplied thrice in the first 4 months of 2021 compared to the last month of the previous year.
What is RDOS?
Ransomware-related service denial (DDoS) attacks have gained popularity in recent years. Recent examples range from banking and financial institutions to hosting providers, online gaming services, and service software (SaaS) businesses. Unfortunately, if even one high-profile victim entrusts attackers by paying a ransom, these types of attacks tend to increase in frequency. RDoS attacks have increased as cyber criminals continue to look for and benefit from more efficient ways to attack systems.
When confronted with the costs associated with stopping their business as a result of a successful DDoS attack; some organizations may believe that paying a ransom demand reflects good value for money. This is a high-risk strategy that gives no assurance that an attack won’t be launched. Thus, emphasizing the dangers these attacks pose to businesses and learning how to effectively defend against them is critical.
What is DDOS Attack?
A distributed denial of service (DDoS) attack attempts to overload an application, website, or network resource to the moment where authorized users are unable to connect to it. DDoS attacks flood their targets with junk network traffic, similar to a traffic jam on the highway. Attacks will be “distributed,” which means they come from multiple sources (spoofed sources), attempting to make them more difficult to stop than a single-source denial-of-service (DoS) attack.
DDoS attacks can have a significant negative impact on an organization’s operations. Any downtime results in a revenue loss for many businesses. If an organization is offline for an extended period of time, it may lose credibility. The payment of a lending charge to the person or group who threatens is never a good idea.
How does RDoS attack work?
The majority of DDoS ransom attacks begin with an attacker sending a ransom note to the target, threatening the organization. Occasionally, an attacker will process a small demonstration attack to demonstrate their seriousness prior to sending a ransom note. If the threat is legitimate and the attacker chooses to act on it, the following steps are taken:
1. The attacker initiates the attack by transmitting attack traffic to the target. They could be employing their own botnet or contracting with a DDoS service to plan an attack. Additionally, multiple individuals working cooperatively can generate attack traffic via DDoS tools. Attack traffic can target the OSI model layers 3, 4, or 7.
2. As a result of the attack traffic, the targeted application or service either slows down or crashes completely.
3. The attack will continue until the resources of the attacker have been exhausted, or the attack can be stopped for another reason, or the target mitigated. Methods of mitigation include rate limiting, IP blocking, blackhole routing or DDoS protection; the first three are difficult to deploy for attacks that have been widely distributed.
4. The attacker may reintroduce payment demands, carry out additional attacks, or both.
The Ransom in RDOS Explained
A DDoS ransom note is a message sent by a malicious party to a business demanding money in exchange for not carrying out a DDoS attack. These are often emailed. Occasionally, the attacker will send multiple messages, each of which contains additional information about their specific threats or demands.
What they say?
A DDoS ransom note can contain a variety of threats:
- The malicious party may claim responsibility for a prior DDoS attack and threaten to launch another.
- They could claim credit for a DDoS attack currently underway against the target.
- They may make a threat of a future DDoS attack, either at a specified time or at an unspecified time in the future.
What they claim?
To make the threat appear more serious, the attacker may claim to be able to launch a DDoS attack of a specified size and duration. These assertions aren’t always true: just because someone claims they can launch a 24-hour 3 Tbps attack doesn’t mean they have the resources to do it.
Who they are?
To lend credibility to their threats, the attacker may claim affiliation with well-known “hacker” groups such as Fancy Bear, Cozy Bear, Lazarus Group, Armada Collective, or others. These assertions may be true, but verification is difficult. It could be a bluff or a copycat attempt.
What they need?
The ransom note will demand payment in some way. While Bitcoin is the most frequently requested method of ransom, the attacker may also request payment in another cryptocurrency or a state-sanctioned currency (dollars, euros).
How to deliver?
At some point, they typically request a specific sum of money and give instructions on how to deliver it.
When the need?
Finally, in order to emphasize the urgency of their demand and increase the likelihood that the targeted party will cooperate, the ransom note may include a strict deadline for delivering the ransom prior to the threatened attack commencing or for terminating the current attack. Some attackers add that the amount of payment required increases every hour or day after the time limit.
Difference Between Ransom DDos and Ransomware
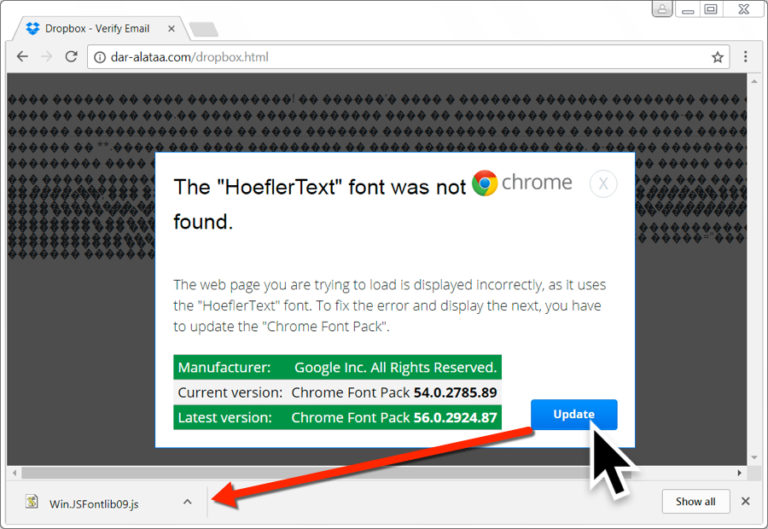
DDoS attacks are increasingly being used as cover for more sinister network intrusions, such as ransomware. DDoS attackers are becoming more advanced; their goal is no longer to cripple a website but to distract IT security personnel with a low-bandwidth, sub-saturating DDoS attack. These attacks are typically less 5 minutes and low in volume, which means they can fly under the radar, undetected by some DDoS protection systems. Latency and service interruptions are all tangible consequences of a successful DDoS attack, whether ransomware-related or not.
Ransomware attacks are another form of online extortion that is becoming more prevalent. Ransomware is malicious software that encrypts an organization’s systems and databases, preventing them from being used. After encrypting the organization’s systems, the attacker will demand payment in exchange for decrypting them. Ransomware must infiltrate a business’s internal systems or network in some way; malicious email attachments used in conjunction with phishing attacks are a common threat vector.
As we all know, it only takes a few minutes for an attack to knock traditional security infrastructure like firewalls and intrusion prevention systems (IPS) offline; in effect, the network doors are wide open. While IT staff scrambles to address brief network outages or system slowdowns; hackers can map a network and install ransomware using automated scanning or penetration techniques. Corero continues to see an increasing number of DDoS attack attempts directed at its customers. In the first quarter of 2017, Corero customers were subjected to an average of four attack attempts per day. To add to the frequency of DDoS attacks, 80 percent of attack attempts had a bandwidth of less than 1Gbps. There is also cause for worry about the average duration of DDoS attacks, as 71 percent of these attacks took 10 minutes or less.
A Practical Example of Ransom Denial of Service Attack
In 2020, a wave of ransom-distributed denial-of-service (DDoS) attacks targeted over 100 financial services firms all over multiple countries.
The attacks spread methodically across Europe, North America, Latin America, and Asia; affecting dozens of financial sector organizations in each region, according to the Financial Services Information Sharing and Analysis Center (FS-ISAC). Banks, exchanges, payments companies, payroll companies, insurance companies, and money transfer services were all targeted. Each time, the attacker sent targets an extortion note threatening to disrupt their websites and services with a DDoS attack if they did not pay the demanded ransom. The FS-ISAC said in a statement; this week that the threat’s impact was significantly mitigated by members’ willingness to share information about the unfolding threat via the FS-ISAC Threat Intelligence Exchange.
No FS-ISAC member who received the threat reported paying the ransom, according to the information sharing center. As globalized attack waves develop and become more complex, the statement said, “cross-border information sharing becomes far more essential in cyber defense.”
According to the FSISAC’s-analysis of ransom DDoS attacks, the majority of targeted organizations (43% ) were located in the United States or Canada. Around 38% of attacks targeted banks, credit card issuers, and other financial companies across Europe, the United Kingdom, the Middle East, and Africa; 15% targeted organizations in the Asia-Pacific region; and 3% targeted organizations in Latin America.
A subvertical breakdown of victims revealed that attackers primarily targeted retail banking or consumer banking: these organizations targeted over 40% of DDoS extortion attacks. Other relatively targeted exchanges (15%), payment companies (13%), securities and investment firms (10 percent ).
Some businesses, according to the FS-ISAC, increased their cybersecurity spending in response to attacks. “Improved sharing of threat intelligence by FS-Intelligence ISAC’s Exchange was also important in protecting against all these attacks,” said the information sharing center.
This week’s wave of attacks reported by FS-ISAC matches multiple security vendor findings indicating a significant spike in last year’s ransom DDoS attacks, especially in the second half.
In the fourth quarter, adversaries posing as well-known advanced persistent threat groups—such as North Korea’s Lazarus Group and Russia’s Fancy Bear and Cozy Bear groups—launched a barrage of ransom DDoS attacks. News from Neustar.
Numerous attacks targeted industries previously avoided by ransom DDoS operators, including financial services, telecommunications, and government. Unlike previous DDoS extortion campaigns, the 2020 attacks were more persistent, advanced, and targeted, according to the security firm. Other vendors, such as Akamai and Cloudflare, reported similarly increased ransomware attacks.
Last year alone, ransom DDoS attacks increased significantly. According to space-monitoring security vendors, the overall number of DDoS attacks increased in 2020, even as the attacks themselves grew larger, lasted longer, and incorporated multiple attack vectors.
I received an Ransom Denial of Service Blackmail. Should I pay the Ransom?
Not at all. Apart from the fact that paying a ransom entails providing money to criminals, it does not guarantee that the attackers will cease their activities. On the contrary, an organization that pays a ransom is a more desirable target because it has demonstrated a willingness to comply with the attackers’ demands and is thus more likely to comply with future demands. Additionally, the more money an attacker obtains, the more effectively they can finance their extortion operation, thereby increasing their capacity for future attacks.
Businesses that receive DDoS ransom demands should report to appropriate law enforcement authorities. Then it will implement safeguards to protect themselves from future attacks if the attackers carry out their threats. Cloudflare DDoS Protection is one such service that protects against DDoS attacks. We must take security threats seriously. But not all DDoS ransom threats are real. Typing and sending a brief email is relatively easy. Maintaining and activating a large network of compromised devices (called a botnet) for large DDoS attacks requires significantly more resources.
Nonetheless, numerous DDoS-for-hire services are provided on the dark web, and one attacker may contract to carry out the attack. Naturally, this requires the attacker’s money – which they can get through threats of DDoS ransom. Typically, ransom DDoS attacks are a game of numbers. Whether the party demanding the ransom can carry out their threats, they count on a small percentage of their targets to pay the ransom.
Rather than trying to determine the credibility of the threat, the safest course of action is to use a DDoS protection service that can keep a web property or network online, regardless of threat.
How to Prevent Ransom DDOS?
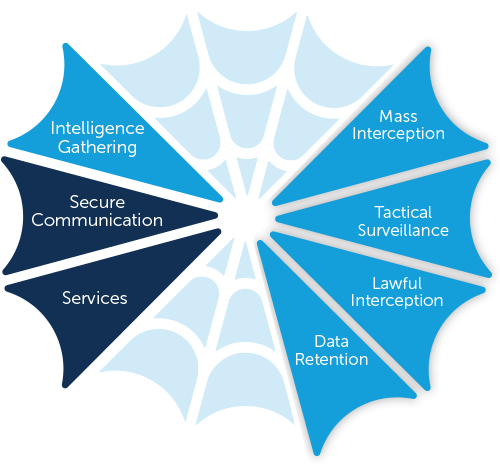
Sadly, most cyber-security solutions focus on recovery, not defeat, from criminal attacks. The Ddos protection landscape has developed to automatically and instantly manage these attacks to remove the threat to your company. Enterprises should be more proactive in preventing ransom attacks and one way to do so is to install DDoS protection solutions that detect and block even the smallest 24×7 DDoS attacks automatically. IT security teams will then have complete visibility into network intrusions.
1.Know the signs of a DDoS attack. As previously stated, short duration, low-volume attacks serve as a stress test for your security perimeter, identifying security vulnerabilities. Analyze your network traffic patterns and look for solutions that can detect DDoS attack traffic in real time and immediately remove the threat..
2. Create a plan for DDoS resiliency. You should include technical competencies in these resiliency plans. Including a comprehensive plan outlining to keep business operations running in the event of a successful denial of service attack. To ensure that key stakeholders are notified, an incident response team should establish. They should document methods of communication with the business, including key decision-makers across all branches of the organization.
3. Combine time-to-mitigation with successful threat defense. When dealing with a DDoS attack, time is of the essence. Service availability cannot be guaranteed if a DDoS attack is not mitigated within minutes. Time-to-mitigation must be a critical factor in your decision-making process as you develop your resiliency plan and select your method of DDoS protection.
4. Check more than one box. Even firewalls that claim to have built-in anti-DDoS protection have only one method of preventing attacks: the use of indiscriminate thresholds. When the threshold value is exceeded, all applications and users that use that port are blocked, resulting in an outage. Attackers are aware that this is an effective method for blocking both good and bad users. The end goal of denial of service is achieved because network and application availability is impacted.