[WARNING] Are you using the Safest WiFi Security? WEP, WPA, WPA2, WPA3, WPS Difference Explained
Is your WiFi Network safe from Hackers? Otherwise, you will be in trouble. WEP, WPA, WPA2, WPA3, WPS Difference Explained!
Articles related to Penetration Testing

Is your WiFi Network safe from Hackers? Otherwise, you will be in trouble. WEP, WPA, WPA2, WPA3, WPS Difference Explained!

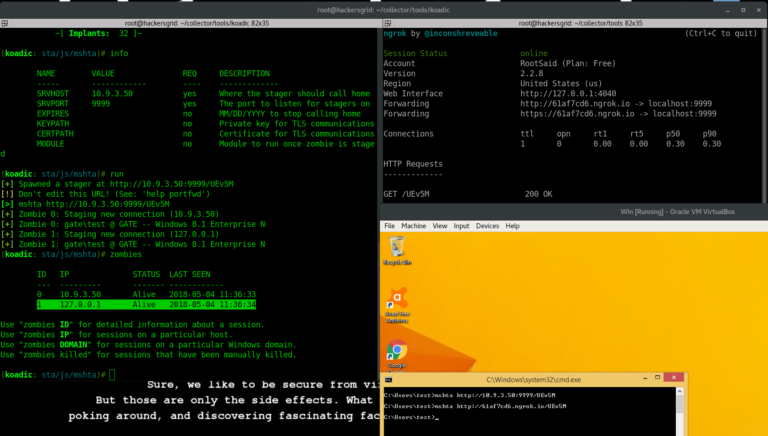
Hackers are finding creative ways for exploiting Log4J Vulnerability and using it to create backdoor, cryptomining and to create botnet.

Log4Shell, formally known as CVE-2021-44228 vulnerability could allow an attacker to execute malicious code on the vulnerable system by sending it a single string of text.

Each year, millions of people are tricked by phishing attacks. See why they happen and how to protect your company from them in this article!

Hacking is a mindset defined primarily by an adventurous spirit about how things work. It entails a readiness, even an eagerness to explore, learn, and experiment. Ethical hacking, also called penetration testing, is a process in which an individual attempt to compromise the security of a channel or system to identify a vulnerability or danger….

What is RDDOS Attacks? Find out everything you need to about the rising Ransom Denial of Service and how to defend against it.

What is Smishing? Check your phone right now. You’re sure to see at least a couple of unsolicited messages in your inbox. Dangers of Smishing
Introduction Whenever we speak of the advancements in artificial intelligence, at least some of us think of a horrific future where machines take over the world. But instead of hostility, have you ever thought of how beneficial it is to use AI to prevent some of the very real threats the cyber world faces today?…
New WordPress Malware Disables Security Plugins – A PHP written software, which continuously works for disabling active security plugins.
Introduction Botnets are now one of the series issues we are facing today. They are widely used by hackers and cybercriminals to perform various types of cyberattacks. Introducing an awesome tool to assess the strength of your security measures and fight against botnet attacks. What is Botnet? Bot-Net – Network of Bots. What are bots?…